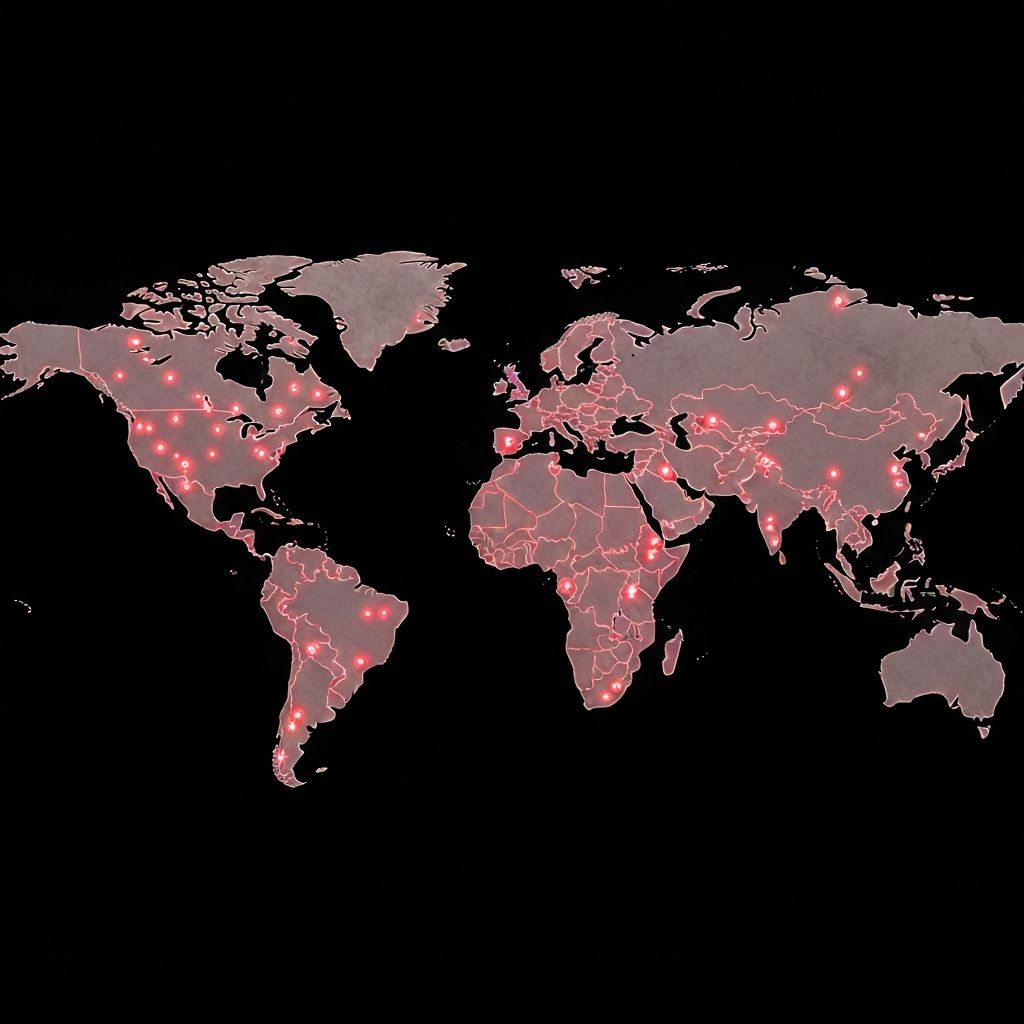
On the morning of May 12, 2017, computers around the world began displaying a red screen with a message: your files have been encrypted, pay $300 in Bitcoin to get them back. Within hours, over 200,000 machines in 150 countries were infected.
WannaCry wasn't the first ransomware attack, but it was different. Most ransomware requires someone to click a malicious link or open an infected attachment. WannaCry didn't need that. It was a worm—a self-spreading piece of malware that could jump from computer to computer across networks without any human interaction.
And it moved fast. Terrifyingly fast.
The Day Everything Stopped
Britain's National Health Service was among the first major casualties. Computers in hospitals across England suddenly locked up. Doctors couldn't access patient records. Appointments were cancelled. Ambulances were diverted. Staff resorted to pen and paper while patients waited, unsure what was happening.
At train stations in Germany, the departure boards showed the ransom note instead of train times. FedEx's systems went down. Renault halted production at several factories. Telefónica, one of the world's largest telecommunications companies, told employees to shut off their computers immediately. Russia's Interior Ministry reported over 1,000 infected machines.
By the end of the first day, the attack had touched nearly every continent. Total damages would eventually be estimated between $4 billion and $8 billion worldwide.
How It Worked
WannaCry exploited a Windows vulnerability called EternalBlue. This vulnerability allowed the malware to spread through a protocol called SMB (Server Message Block), which Windows computers use to share files and printers across networks.
Here's the critical part: Microsoft had released a patch for this vulnerability in March 2017—two months before the attack.
The EternalBlue exploit was originally discovered by the NSA and was part of their cyber arsenal. A hacking group called the Shadow Brokers leaked it to the public in April 2017. Once it was public, anyone could use it. The WannaCry creators did exactly that.
So the timeline looked like this:
- March 14, 2017: Microsoft releases security patch MS17-010
- April 14, 2017: Shadow Brokers leak the EternalBlue exploit
- May 12, 2017: WannaCry attack begins
Organizations had nearly two months to install a critical security update. Many didn't. And they paid the price.
The Accidental Hero
WannaCry's spread was stopped—at least partially—by accident. Marcus Hutchins, a 22-year-old security researcher from England, was analyzing the malware when he noticed something strange. The code was trying to connect to a specific domain name that didn't exist: a long, random string of characters ending in .com.
Curious, he registered the domain for about $10. What he didn't realize was that this domain was a kill switch—a failsafe built into the code. Once that domain went live, WannaCry would check it before encrypting files. If the domain responded, the malware would stop spreading.
By registering that domain, Hutchins accidentally saved countless organizations from infection. But the damage was already done for hundreds of thousands of victims.
Why Windows XP Mattered
One detail that stood out in the aftermath: many affected systems were running Windows XP, an operating system Microsoft had stopped supporting in 2014. When software reaches "end of life," it stops receiving security updates. Any new vulnerabilities discovered after that point remain unpatched forever.
The NHS, for example, was still running Windows XP on many of its computers. When the attack hit, those machines had no protection. Microsoft actually released an emergency patch for XP after WannaCry—an extraordinary step that highlighted just how serious the situation was.
Running unsupported software is like driving a car with a known brake defect because you don't want to pay for the repair. Eventually, something bad happens.
The Lessons That Still Apply
WannaCry happened in 2017, but the lessons are timeless. Here's what the attack taught us about security fundamentals:
Updates Are Non-Negotiable
Every infected system that had installed the March 2017 patch was protected. Every system that hadn't was vulnerable. That's the entire story. Security updates exist because vulnerabilities are discovered constantly. Delaying updates is gambling with your data.
End-of-Life Software Is a Liability
If you're running software that's no longer supported—whether it's an old operating system, an abandoned plugin, or a legacy application—you're accumulating risk every day. Upgrade, migrate, or find alternatives. The cost of upgrading is almost always less than the cost of a breach.
Network Segmentation Limits Damage
WannaCry spread laterally across networks, jumping from one vulnerable computer to the next. Organizations with proper network segmentation—where different parts of the network are isolated from each other—contained the damage. Those without segmentation watched the infection spread everywhere.
Backups Are Your Last Line of Defense
Organizations with recent, working backups could restore their systems without paying the ransom. Those without backups faced a terrible choice: pay criminals and hope for the best, or lose everything. Many paid. Many still didn't get their data back.
The 3-2-1 backup rule applies here: three copies of your data, on two different types of storage, with one copy offsite. And critically—test your backups regularly to make sure they actually work.
Who Was Behind It?
In December 2017, the US, UK, and Australia officially attributed WannaCry to North Korea's Lazarus Group, a state-sponsored hacking operation. The attack was apparently intended to raise money for the regime, though it only netted around $140,000 in Bitcoin ransoms—a tiny fraction of the billions in damage it caused.
This highlighted another uncomfortable truth: cyberattacks can come from nation-states, not just random criminals. The line between cybercrime and cyberwarfare is increasingly blurry.
What This Means for Your Business
You might think your small business isn't a target for something like WannaCry. But automated attacks don't discriminate. The malware didn't know or care whether it was infecting a hospital, a factory, or a small retail shop. It just looked for vulnerable systems.
Protecting yourself isn't complicated:
- Enable automatic updates on all systems
- Replace any software that's no longer receiving security updates
- Maintain regular, tested backups stored separately from your main systems
- Train employees to recognize suspicious emails and links
- Consider network segmentation if you have multiple systems
WannaCry succeeded because of basic security failures—failures that were entirely preventable. The organizations that escaped unharmed weren't lucky. They were prepared.
The Bottom Line
WannaCry was a wake-up call that echoed around the world. It proved that cybersecurity isn't just an IT problem—it's a business survival issue. When hospitals can't access patient records and factories grind to a halt, the consequences go far beyond lost data.
The attack also proved something encouraging: basic security practices work. Every organization that had installed a two-month-old patch was protected. Security doesn't require massive budgets or cutting-edge tools. It requires attention and consistency.
If there's one takeaway from WannaCry, it's this: update your software. Today. Right now. Don't wait for the next global cyber pandemic to remind you why it matters.